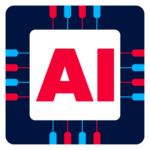
CPTA v2 Lab Architecture
Cyber Range Lab Highlights
Blue Team Highlights
- Hands-on investigations on various Security solutions [SIEM | IR | Network Monitoring | Threat Intel]
- Understand the working behaviour of various offensive operations to perform better defend against real threats
- Enhance the real time investigation skills
- Develop and refine their cybersecurity skills, including network monitoring, intrusion detection, incident response, and security configuration management.
- Custom rule creation for multiple attacks
Red Team Highlights
- Perform Breach and attack simulation
- Understand the working behaviour of Security Solutions and detection engineers to bypass it
- Enhance Stealth Red Team skills by analysing Blue Team activities
- Simulate Attacks on various environments [Network, Web, Host And Active Directory]
The courses contents are divided across 5 sections listed below:
Introduction to Purple Teaming
- Understanding the concept of purple teaming
- Roles and responsibilities of a purple team
- Key concepts in Purple Teaming
Offensive Security Techniques
- About Red Teaming
- Red Team Lifecycle
- Adversary Simulation Using MITRE ATT&CK Framework
Defensive Security Strategies
- About Blue Teaming
- Adversary Detection using MITRE D3FEND Framework
Defensive security tools and technique
- SIEM
- Incident Response
- Threat Intelligence
- Incident Management
- OSQuery
- Network Monitoring
Security testing methodologies
- Web Exploitation And Detection
- Network Exploitation And Detection
- Host Exploitation And Detection
- AD Exploitation And Detection
- SIEM: ELK + WAZUH
- Incident Response: Velociroptor
- Threat Intelligence: MISP
- Incident Management: The HIVE
- IDS/IPS: Suricata + IDS Tower
- Network Monitoring: Akrime Moloch
- Real Time Investigation: OSQuery
Pre-requisites
Following are the requirements:
- Understanding of OS, Web & Network based attacks
- Understanding about SIEM Solution
- Familiarity with Command line basics
Target Audience
Designed specifically for Intermediate level of knowledge and experience in Red Team and Blue Team
- Penetration Testers
- Internal Red Teams
- SOC Analyst
- Forensics Enthusiasts
- Detection Engineers
- Threat Hunters
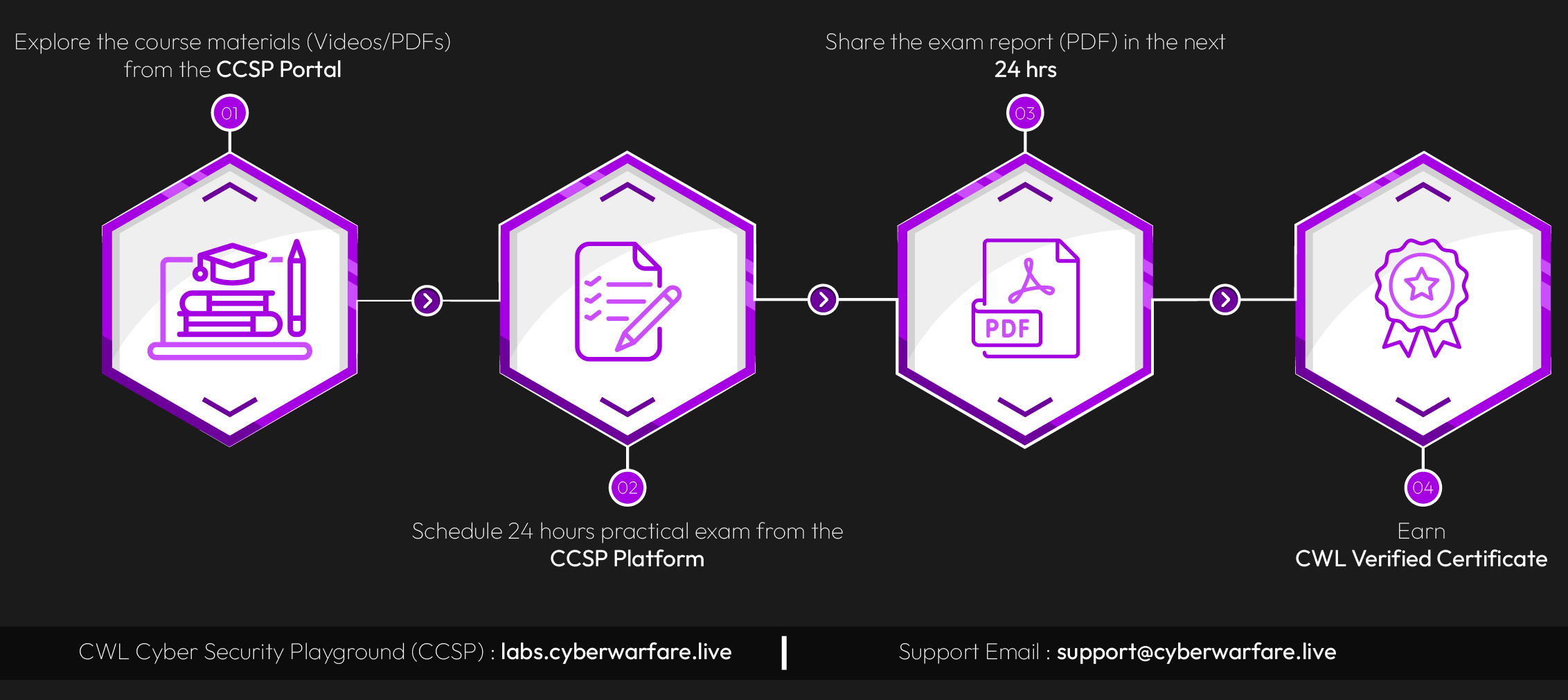
Premium Version
Certified Purple Team Analyst Premium Edition
$199
Top Features of Premium Edition:
- 100 + PDF pages & 2+ Hrs HD Videos
- 300+ PDF Pages Exercise Write-Ups
- 30 Days Lab Access with Technical Support
- CW Labs Platform Access [Automated Lab Access]
- 30+ Unique Practical Purple Team Exercises
- Web, N/W, Host & AD Domains Coverage
- 6+ Blue Team Solution Integration
- Custom SIEM Rule Creation & Play Books
- Verified Accredible Badge + Module Based Badges
- Get Lifetime Access